Simplify Forefront TMG Migration By Web Chaining To An Upstream Proxy
by

Etienne Liebetrau
Microsoft Forefront TMG's web filtering capabilities officially ended on 31 December 2015. However, a large portion of Forefront TMG users have not migrated to an alternative platform or are struggling to complete their migration. This article will describe how to use Forefront TMG's web chaining feature to use an upstream proxy to take over the web filtering duties until your migration is complete. This assumes you have a replacement proxy server ready for use but you have not been able to migrate your user base yet.
The problem with changing proxy servers
In most environments you need to explicitly define a proxy server to be used by internet accessing applications. In most cases, these are browsers such as Internet Explorer, Chrome and Firefox but there are many more.
Java is a huge culprit for causing proxy server migration issues. Depending on the version you have installed, it may or may not cache proxy settings, it may or may not authenticate correctly, and it may or may not work. The same goes for other applications such as Skype and iTunes.
Another concern for corporate environments are server services that require Internet access, such as WSUS (Windows Server Update Services), SCCM (System Center Configuration Manager), and Antivirus management servers that need to download and distribute virus definition updates. And then of course there are things like Linux servers that have been hard coded with the IP address of your old Forefront TMG server.
Basically, if your migration plan is to simply rip and replace Forefront TMG with something else, you are going to have a hard time.
Simplifying Forefront TMG Migration With Web Chaining
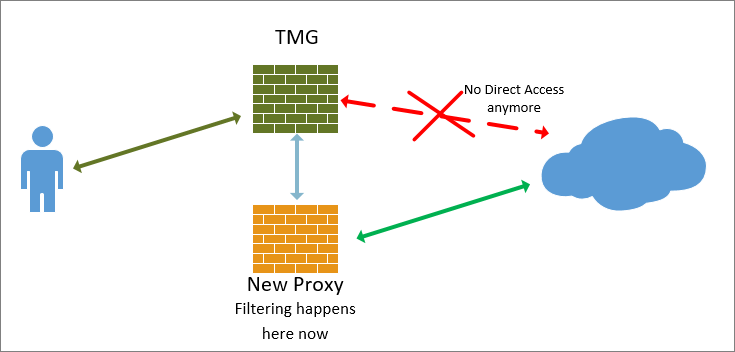
Forefront TMG's Web Chaining feature is normally used when you have a distributed environment where remote sites connect through a private WAN to your primary Internet break out. Placing a local proxy at each remote site allows you to secure and filter requests from that site before it hits the main corporate proxy. Forefront TMG refers to this as an upstream proxy.
Here's the really nice part. The upstream proxy does not have to be a Forefront TMG server. It can be a different type of proxy such as Sophos UTM, or whatever proxy you intend to migrate to. The proxies also do not have to be in separate networks - they can be right next to each other.
Based on the specified rules on Forefront TMG, it will forward Internet requests to the upstream proxy, which then applies its own set of web filtering rules, before retrieving or denying the web request.
The advantage here is you do not initially need to migrate all users, devices and servers to use your new proxy. This can be done gradually because Forefront TMG's security is now reinforced by a web filtering and malware scanning proxy.
Creating Your Forefront TMG Web Chaining Rule
The configuration below needs to point to your new proxy and match its settings as far as IP, ports and authentication is concerned. The upstream proxy also needs to allow the traffic through. It is advisable to configure the upstream proxy to do this before implementing the following.
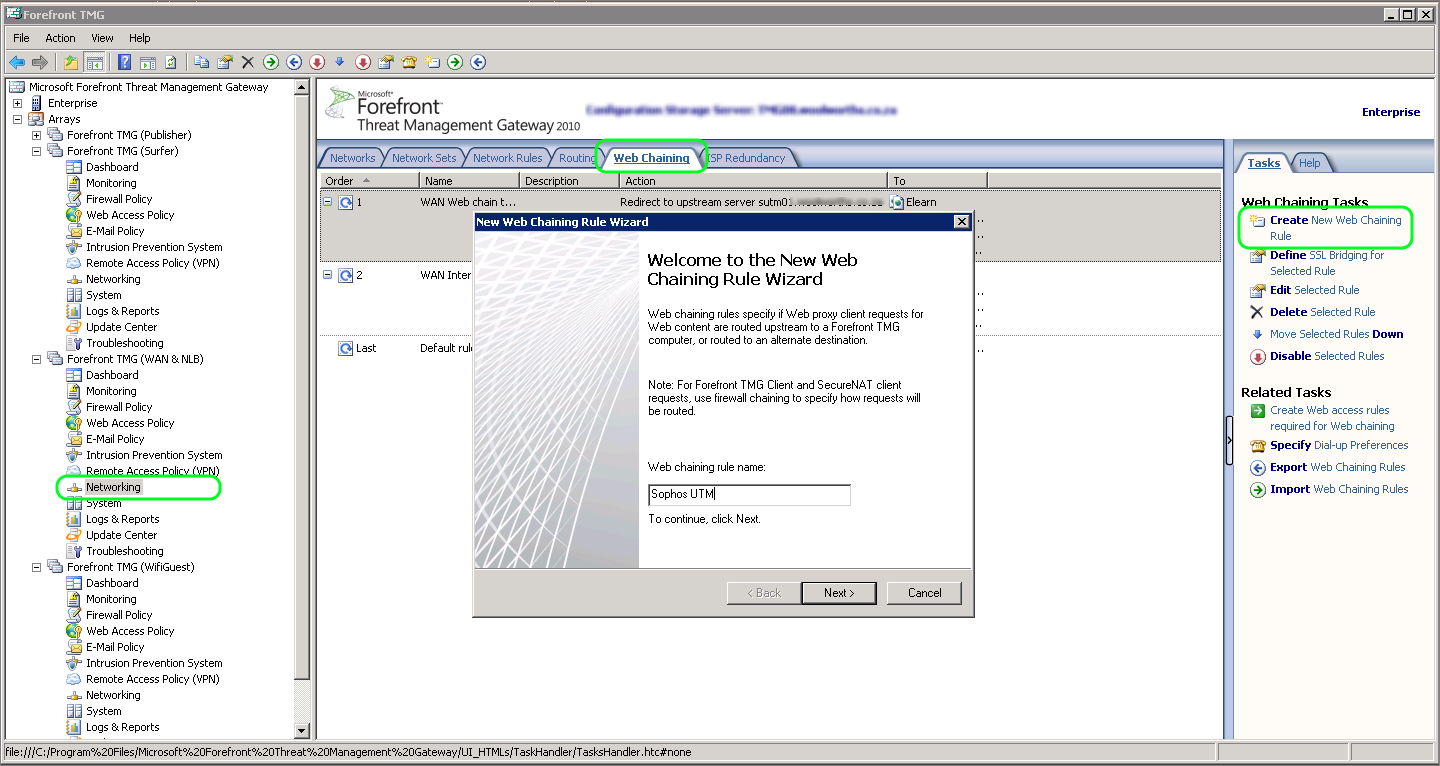
From the Forefront TMG management console, select Networking | Web Chain
Click Create New Web Chain Rule from the Task Pane
Specify a name and click Next Add the External Network as a Destination and click Next
Select Redirect requests to a specified upstream server and click Next
Specify the Server, Ports and optionally set a User Account. Click Next.
The Backup action should be set to Ignore Requests. Click Next and Finish.
Checking the Traffic flow
You will now be able to observe if the web traffic is being forwarded to the upstream proxy by running a Live Query in logs and reports and checking the destination IP address. This will no longer be the public IP address of the site, but instead, it will be your upstream proxy server.
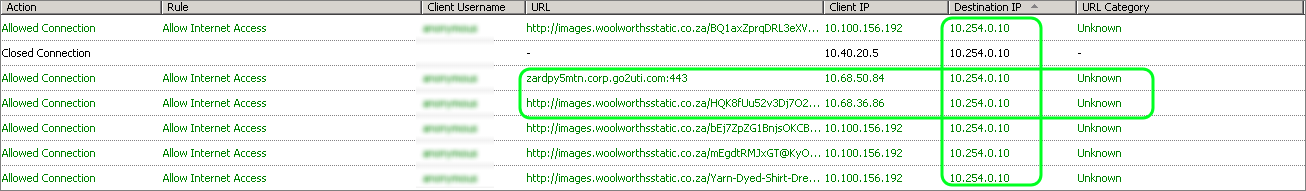
You should also see corresponding traffic on your upstream proxy. You will be able to distinguish it from clients connecting directly to your new proxy since the source for the web chained traffic will be the Forefront TMG server. The same is true for the username if you specify one. It is not the users credential but rather the one specified by the web chain.
Affects on logging and reporting
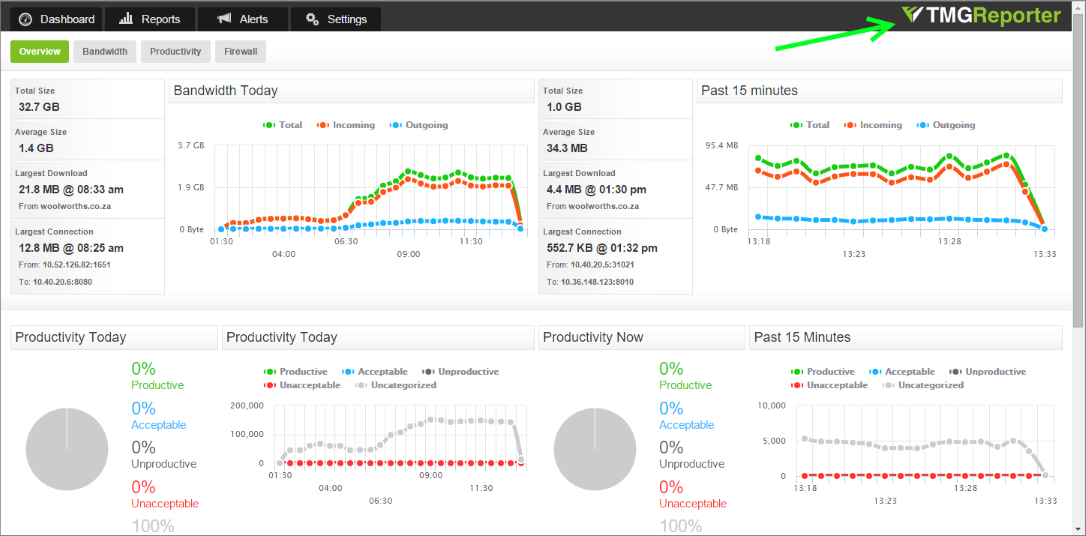
As mentioned above, all of the traffic from Forefront TMG will now be seen as a single user or a single device. This will not affect your logging and reporting from a TMG perspective. The image below still shows that traffic is being logged and reported on as if TMG is requesting the sites directly.
However, as Forefront TMG's Web Protection services is no longer in play, categories will not be logged, and Fastvue TMG Reporter's productivity based reports, dashboards and alerts will no longer work. For more information about what to do with TMG's URL filtering and category-based rules, see our article: Finding a Forefront TMG replacement is more urgent than you thought.
Your new proxy on the other hand will not have insight into who the individual users are. This will only be visible for clients using the proxy directly and authenticating against the new proxy. Everything still going through Forefront TMG effectively becomes one user.
Web Chaining Limitations
The Web chaining feature can get you out of a bind if you’re still using it as a secure web gateway, but it does have some limitations. You can specify multiple chaining rules, but the flexibility of the rules aren’t great. You cannot for instance forward requests from a specific user but not another.
The same limitation is true for the source. You can be selective when it comes to the destination, but you will not be able to use URL categories due to Microsoft Reputation Service’s end of life.
Suggested Upstream Proxies
For many users, Sophos UTM provides the best feature for feature replacement for Forefront TMG but there are many viable alternatives. As long as the replacement device supports standard explicit proxy connections, you should be able to use it as an upstream proxy.
If you are currently using Fastvue TMG Reporter and would like to keep reporting continuity, we do have sister products for the popular Forefront TMG replacements, with more on the way.
You’re also welcome to suggest another.
If you are an existing customer, Fastvue has special migration pricing to move to a new Fastvue Reporter or WebSpy Vantage product. Just get in touch with our friendly sales folk.
Conclusion
If you are lagging behind in your Forefront TMG migration, or you are struggling to get all devices migrated, Forefront TMG’s web chaining feature may help smooth out the process for you. It is significantly more secure than simply allowing traffic through the Forefront TMG without any of the deprecated web filtering protection.
Try TMG Reporter free, or learn more
- Share this storyfacebooktwitterlinkedIn