Testing Sophos SSL VPN Performance - UDP or TCP?
by

Etienne Liebetrau
When configuring a Site-to-Site VPN on your Sophos SG or Sopho XG, you are presented with an option to select either TCP or UDP as the transport protocol. The configuration page hints that UDP provides better performance, so I thought it would be interesting to test the SSL VPN performance over both UDP and TCP protocols and find out which one is faster!
Since everyone wants better performance, the choice for UDP seems obvious, but as you will discover, there are more factors to consider than just the protocol itself.
TCP and UDP Basics
TCP is a connection orientated protocol. This means a three-way handshake needs to occur before packets are sent, and delivery is "guaranteed". That means that the server gets an acknowledgement when the sent packets have been received, and if the acknowledgement does not come through, the packets are re-sent. TCP is therefore preferred for data integrity.
UDP, on the other hand, is a connectionless protocol. This means packets are thrown out with no protocol level reliability. A packet is sent out but there is no acknowledgement of them being received. UDP is theoretically faster since it does not require 3-way handshakes and packet acknowledgement. UDP is useful for applications such as video streaming where dropping a packet here or there is an acceptable trade-off for the overall speed improvement. UDP is therefore preferred for speed if the application can handle error correction.
Using UDP or TCP for SSL VPNs
Unlike direct client-server communications, VPNs work by wrapping and encrypting the client-server packets with VPN headers or metadata. VPN traffic is therefore slightly 'bigger' than native traffic.
The VPN will take the traffic, TCP or UDP and wrap it in its own VPN protocol, which as you see above, has the option of being TCP or UDP. You could, therefore, have a HTTP session that uses TCP being wrapped in UDP packets being sent over the VPN.
In such a case, the VPN is not responsible for error correction. This is left to the web server and client.
If we flip this example around, imagine a protocol like DNS (UDP) being transmitted over a TCP SSL VPN. In this case, the VPN will take care of error correction.
Error correction needs to happen somewhere, the burden either lives with the VPN or with the application server and client.
How UDP or TCP affects SSL VPN Compatibility
SSL VPNs over TCP look identical to HTTPS web traffic. Firewalls and proxies therefore typically do not have an issue handling the traffic. Countries or regions that may block VPNs typically block IPSEC tunnels but not TCP SSL VPNs because it would break HTTPS and therefore most of the Internet.
SSL VPN over UDP still attempts to connect to the VPN server on port 443, but unlike HTTPS traffic that uses TCP as a transport protocol, it uses UDP. Some firewalls and proxies may flag this as suspicious and drop the traffic. It can also be seen as peer-to-peer traffic (which it actually is) and again be dropped.
So by now, it may seem that TCP is the preferred transport protocol as the VPN takes care of error correction, taking the load off the clients and TCP ensures a higher level of compatibility for more diverse environments. BUT – Sophos says UDP is faster and everyone likes faster, So let’s answer the last concern.
Testing Sophos SSL VPN over TCP or UDP - Which is Faster?
I am going to start off the section by saying that everyone's environment is different. This is purely a simple, indicative test along with the results.
- My test base is two virtual Windows servers behind two virtual Sophos XG appliance with an SSL VPN Site-to-Site established.
- The Sophos XG devices are on the same virtual switch. This is, therefore, a high-speed reliable WAN configuration.
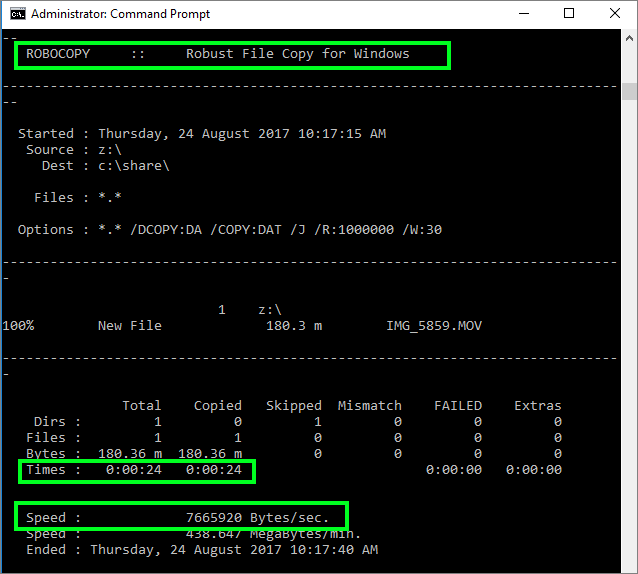
- The test is a file copy operation using robocopy between the two Windows boxes. I prefer this tool as it accurately measures time and throughput.
- I performed the same test three times for each TCP and UDP protocols.
If we place the two Windows boxes on the same subnet with no firewalls in between we get a throughput of 71,741,160 B/s so this is the absolute maximum.
If we place one of the servers behind a firewall and do the same test (without a VPN) we get an average throughput of **9,581,763 B/s ** This is a significant drop in performance. This is because firewall and IPS functions are being applied to the traffic, as well as an extra hop.
Placing both Windows servers behind their own firewall and establishing the VPN we get the following:
| Protocol | Bytes Per Second | Average Time Taken |
|---|---|---|
| TCP | 8,257,675 B/s | 22.5 seconds |
| UDP | 8,255,688 B/s | 22.5 seconds |
So in a fairly anti-climactic way, there is no noticeable difference. If anything, UDP proved very slightly slower on average. Having said that, the single fastest transfer of 8,390,679 B/s was achieved with UDP. The graph below indicates just how close it is over the course of the three runs per configuration.
The Real Performance Hog
During testing, I had a massive drop in performance when first connecting the VPN. This is because the traffic was now going through two IPS scans (one on each firewall). Since it is the IPS same engine on both sides, there is absolutely no benefit from doing this. Dropping the IPS on one side of the VPN got performance back up to where it is expected. I want to say HOG because Sophos uses Snort for the IPS functionality and its logo/mascot is a hog or pig :)
If you're concerned about your VPN or network performance, I recommend tweaking your IPS settings to improve performance, over worrying about TCP or UDP for your VPN protocol.
Conclusion
At this point in time, my recommendation is to stick with TCP as your SSL VPN transport. Bank the reliability and compatibility and pay more attention to your IPS configuration. Lastly, check your applications, and focus on optimising any internal web applications with technologies such as HTTP2 and dynamic gZip compression.
We would love to hear your feedback regarding Sophos VPN performance in the comments below.
Take Fastvue Reporter for a test drive
Download our FREE 14-day trial, or schedule a demo and we'll show you how it works.
- Share this storyfacebooktwitterlinkedIn
How to Configure Multiple Site-to-Site SSL VPNs with Sophos UTM
Setup a Sophos UTM SSL VPN In 7 Simple Steps!