SonicWall DPI-SSL Logging Issues Affecting Bandwidth Reports
by

Scott Glew
We originally wrote about logging issues introduced in SonicOS 6.2.6.0 where web traffic was logged with enormous size values in the 'Syslog Website Accessed' event, which is the event Fastvue Reporter uses for all web usage reports. A hotfix was released (SonicOS 6.2.6.0-20n–HF176616-1n), but the size values were still logged incorrectly. This time they were logged with incredibly small size values.
SonicWall released another hotfix for this issue (SonicOS 6.2.6.1-25n–HF180023-1n) which works for all traffic going through SonicWall's Content Filtering Service (CFS) which is great... until you enable DPI-SSL.
Update: SonicWall have made a fix available for the issue described below! Woohoo! You currently need to request hotfix 6.2.7.1-23n—HF187283 from SonicWall support.
Issues with DPI-SSL Logging and Reporting
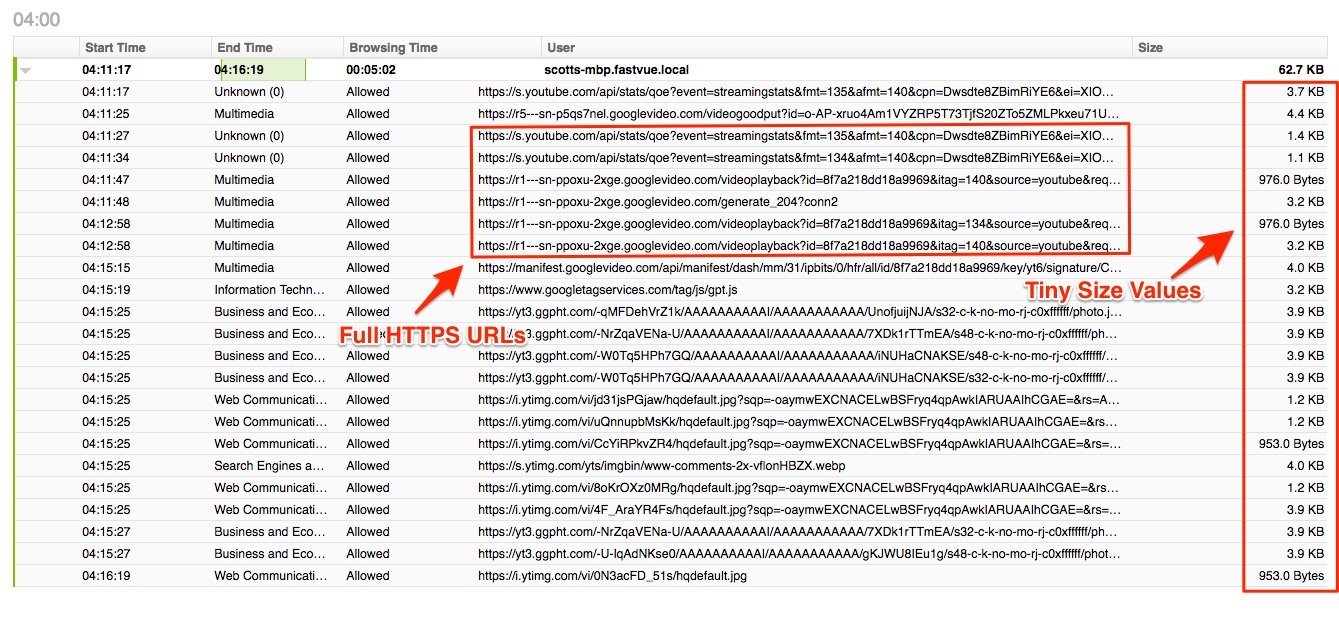
Unfortunately, all traffic going through SonicWall's DPI-SSL feature is still logged with incredibly small size values - only a few bytes for each URL, and it's often the same number of bytes.
This means that you will not see any DPI-SSL traffic in Fastvue Reporter's bandwidth dashboards or reports, as it essentially gets drowned out by all the correctly logged HTTP traffic. It also means that DPI-SSL traffic will never trigger a 'Large Download' alert, even if the file transmitted over HTTPS is hundreds of GBs in size.
The URLs still get logged, so if you run an Activity Report filtered by youtube.com (Origin Domain 'Equal to' youtube.com) for example, you'll see the URLs accessed, but each one will have only a few bytes associated with it.
SonicWall are aware of the issue, and we're told they are working on a fix.
Testing the DPI-SSL Size Logging Issue
Below are some test download files, along with their 'Syslog Website Accessed' log entries. If you would like to test this issue for yourself, enable DPI-SSL, download these files, then checkout the corresponding syslog entries (m=97 events). We recommend using a syslog server that logs the syslog messages to plain text (we have a free syslog server you can use here). You'll notice the rcvd size (recorded in bytes) is much smaller than it should be when accessed with DPI-SSL enabled:
1 MB test: https://s3.amazonaws.com/cdn.fastvue.co/testfiles/1meg.test
id=firewall sn=18B1691F9960 time="2017-02-20 15:05:36 UTC" fw=10.1.1.219 pri=6 c=1024 m=97 app=8460 n=311309 src=192.168.168.133:57417:X0:scotts-mbp.fastvue.local dst=54.231.120.186:443:X1:s3-1.amazonaws.com srcMac=28:cf:da:ef:f9:2c dstMac=c4:ea:1d:50:7e:18 proto=tcp/https op=1 sent=1483 **rcvd=269** dstname=s3.amazonaws.com arg=/cdn.fastvue.co/testfiles/1meg.test appcat="MISC-APPS" appid=1395 code=27 Category="Information Technology/Computers" rule="1 (LAN->WAN)" fw_action="NA"
5 MB test: https://s3.amazonaws.com/cdn.fastvue.co/testfiles/5meg.test id=firewall sn=18B1691F9960 time="2017-02-20 15:02:30 UTC" fw=10.1.1.219 pri=6 c=1024 m=97 app=8460 n=311269 src=192.168.168.133:57068:X0:scotts-mbp.fastvue.local dst=52.216.81.147:443:X1:s3-1.amazonaws.com srcMac=28:cf:da:ef:f9:2c dstMac=c4:ea:1d:50:7e:18 proto=tcp/https op=1 sent=1483 **rcvd=2301** dstname=s3.amazonaws.com arg=/cdn.fastvue.co/testfiles/5meg.test appcat="MISC-APPS" appid=1395 code=27 Category="Information Technology/Computers" rule="1 (LAN->WAN)" fw_action="NA"
10 MB test: https://s3.amazonaws.com/cdn.fastvue.co/testfiles/10meg.test id=firewall sn=18B1691F9960 time="2017-02-20 15:03:20 UTC" fw=10.1.1.219 pri=6 c=1024 m=97 app=8460 n=311279 src=192.168.168.133:57101:X0:scotts-mbp.fastvue.local dst=52.216.81.147:443:X1:s3-1.amazonaws.com srcMac=28:cf:da:ef:f9:2c dstMac=c4:ea:1d:50:7e:18 proto=tcp/https op=1 sent=1483 **rcvd=269** dstname=s3.amazonaws.com arg=/cdn.fastvue.co/testfiles/10meg.test code=27 Category="Information Technology/Computers" rule="1 (LAN->WAN)" fw_action="NA"
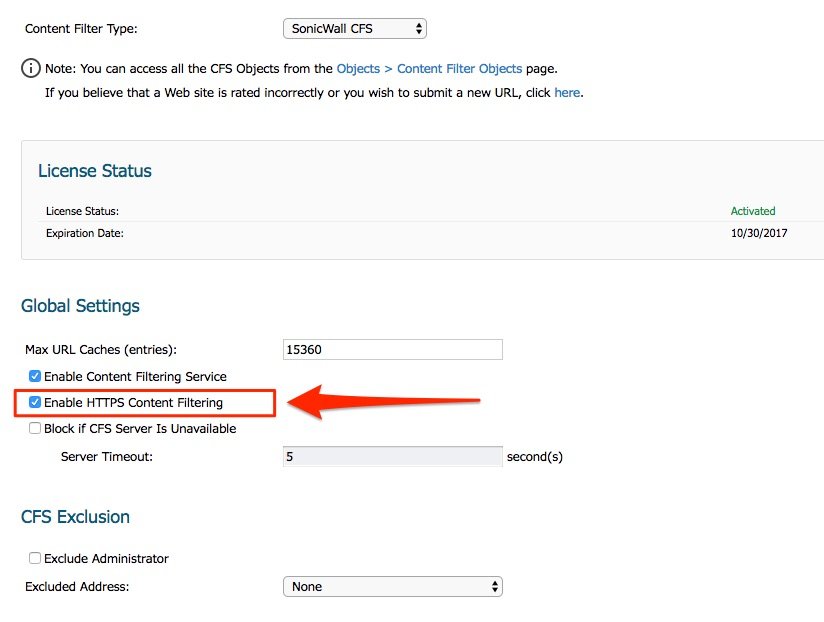
Logging The Correct Size for HTTPS Traffic
In the mean time, if more accurate bandwidth reporting is of higher importance than utilizing the features of DPI-SSL, then you can disable DPI-SSL and check the Enable HTTPS Content Filtering checkbox in Security Services | Content Filter (Note, you cannot have both DPI-SSL and HTTPS Content Filtering enabled at the same time). This means that all HTTPS traffic will go through SonicWall's CFS service, and the rcvd size values will be logged correctly.
Issues with Disabling DPI-SSL
Be aware that if you disable DPI-SSL and enable HTTPS Content Filtering, HTTPS traffic will no longer be decrypted. From a security perspective, this means that threats transmitted over HTTPS will not be scanned or prevented.
From a reporting perspective, it means that the full URLs of HTTPS traffic will not get logged. For example, you will see traffic to www.youtube.com appearing on the Bandwidth dashboards, but you won't be able to see the full video URL someone was looking at in Activity Reports. Likewise, SonicWall will log www.google.com, but not www.google.com/search?q=My+Search+Term so Fastvue Reporter will not be able to report or alert on Search Terms.
Conclusion
At the time of writing this (4th of August 2017) the latest beta release of SonicOS (6.5.0.0-25n) does not contain a fix for this issue. This means that your two options are:
- Enable DPI-SSL and accept the fact that HTTPS traffic will not be displayed in Fastvue Reporter's Bandwidth reports. The good news is your network will be protected by threats transmitted over HTTPS, and full URLs will be logged enabling you to report and alert on Search Terms, video IDs and other information contained in the full URL using Fastvue Reporter.
- Disable DPI-SSL and enable HTTPS Content Filtering so that bandwidth reports in Fastvue Reporter show HTTPS traffic. The bad news is your network will not be adequately protected from threats transmitted over HTTPS, and full URLs will not be logged preventing reports and alerts on Search Terms etc.
We realize that neither option is ideal, but we hope this helps adequately explain the issue so you can make an informed decision. Hopefully, SonicWall will have a fix available soon so that no compromise is needed. We'll keep you posted!
Update: SonicWall have made a fix available! Woohoo! You currently need to request hotfix 6.2.7.1-23n—HF187283 from SonicWall support.
Take Fastvue Reporter for a test drive
Download our FREE 14-day trial, or schedule a demo and we'll show you how it works.
- Share this storyfacebooktwitterlinkedIn
SonicWall Logging Issues Affecting Alerts and Reports on Google Searches
Reporting on WannaCry Ransomware Infected Machines