The Best SonicWall Configuration for Detailed Logging and Reporting
by

Scott Glew
Since releasing Fastvue Reporter for SonicWall in 2016 and seeing it deployed in hundreds of organizations around the globe, we have become very familiar with the effects that various SonicWall configurations and SonicOS firmware versions have on the firewall's logging and reporting.
As a result, here are our main SonicWall configuration recommendations to get the best visibility into user web activity and how your network is operating.
TLDR:
- Ensure SonicWall's CFS is enabled, correctly configured, and the logging options are set correctly for your version of SonicOS (see below).
- Authenticate using AD SSO or LDAP Authentication.
- Enable DPI-SSL to log full URLs for HTTPS traffic.
- Enable Name Resolution.
- Enable Referrer URL logging (SonicOS 6.2.7.1 and above) using the 'Enhanced Syslog' format.
- Block the QUIC protocol
- Disable CFS Fast Scan
Enable Content Filtering Services
SonicWall's Content Filtering System not only blocks inappropriate, unproductive, illegal and malicious web content, but it is also a required service to simply log full URLs and website categories.
With SonicWall's CFS enabled, Fastvue Reporter can report on the websites and categories visited, search terms entered into search engines, the online productivity of your users and more. Even if you don't block anything using CFS, enable the service for logging and reporting of web traffic.
To enable Content Filtering Services, go to Security Services | Content Filter and check the Enable Content Filtering Service. Then create a CFS policy that applies to your LAN network or zone.
SonicWall's Content Filtering Service is a paid subscription service.
To ensure the CFS events are being logged:
- Go to Log | Settings and expand the Log | Syslog section.
- Check the Syslog option for the Syslog Website Accessed events and set the priority to Informational.
- Expand Network | Network | Network Access and check the Syslog option for Website Blocked and Website Accessed events, again making sure the priority is Informational.
We believe the Website Accessed event is now obsolete, and replaced by the Syslog Website Accessed event so don't worry if you see an 'event count' of zero for this event. The Website Blocked event is still in use and needed to report on blocked traffic.
CFS Logging for SonicOS 5.9 to 6.2.5
If you're running SonicOS 5.9 to SonicOS 6.2.5, make sure you check the option to Override Syslog Settings with Reporting Software Settings in Log | Syslog that forces the Syslog Format to be set to Default. Do not choose the 'Enhanced Syslog' option like we recommend for later SonicOS versions as this will result in most of your web traffic appearing as 'Not Rated' in Fastvue Reporter.
CFS Logging for SonicOS 6.2.6 and above
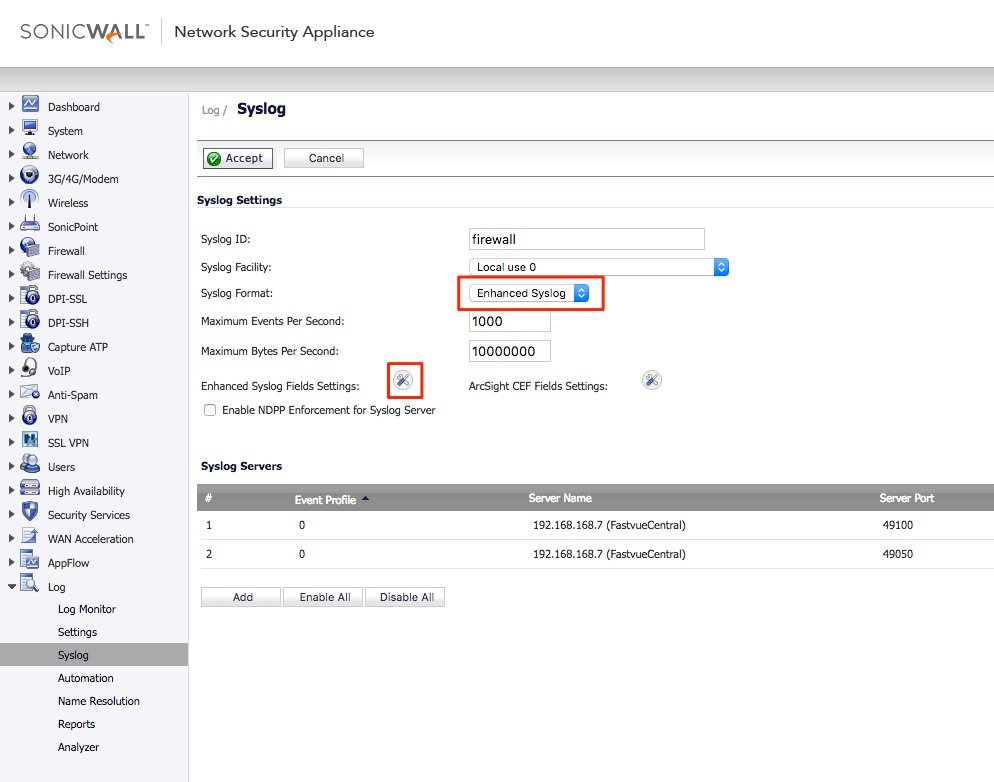
If you are using SonicOS 6.2.6 or above, you can enable Enhanced Syslog in order to log some extra information, such as Source and Destination Zones, Rules and Messages. If you're running 6.2.7.1 and above, you can also log referrer URLs which greatly improves web usage reports (see below). Go to Log | Syslog and change the format to Enhanced Syslog, and make sure the ‘Note (note)’ field is selected.
Authenticate Users
Fastvue Reporter for SonicWall enables easy reporting on Users, Departments, Offices, and Security Groups as defined in Active Directory. However, for any of these feature to work, SonicWall needs to be authenticating users.
Enabling SonicWall's AD SSO or LDAP authentication enables SonicWall to log usernames along with web traffic. Fastvue Reporter for SonicWall then matches these usernames to real people in Active Directory providing the ability to report on people, Departments, Offices, Security Groups and companies as configured in Active Directory.
Without authentication, only IP addresses will be logged, which Fastvue Reporter will attempt to resolve to hostnames.
For more information, please see our article on Reporting on Users, Departments and AD Security Groups.
Also see SonicWall's Knowledge Base article on configuring AD SSO and/or LDAP authentication, or checkout the video below:
Enable SonicWall DPI-SSL
With most of the web now using HTTPS, DPI-SSL is not only an essential technology for protecting your network from threats transmitted over HTTPS, but also for reporting on web usage traffic. Without SonicWall's DPI-SSL feature enabled, only the domain of a website will be logged (e.g. www.google.com) but not the full URL (e.g. www.google.com/search?q=my+search+term). This is important if you need to report on web searches, youtube videos, full web pages, or full virus URLs.
Fastvue Reporter also utilizes full URLs for its Site Clean algorithm to clean 'Junk' urls from your reports. For example, we don't want to clean visits to https://www.facebook.com from your reports, but we do want to clean hits to facebook 'Like' buttons on other pages. Facebook 'Like' buttons come from the URL https://www.facebook.com/plugins/like.php. Without DPI-SSL, SonicWall will only log www.facebook.com, leaving the Site Clean engine unable to clean the 'like' buttons from your reports.
Enabling DPI-SSL can be pain as it requires deploying certificates to all devices that you want to protect and report on. Although this can be relatively easily achieved for devices controlled by AD group policy, it gets tricky for other devices such as BYOD mobile devices, devices on a 'guest' network and for browsers with their own certificate store (we're looking at you Mozilla Firefox!).
In these situations, you can manually email the certificate to users along with installation instructions, post it on an internal website that users can access once logged in (captive portal), or use onboarding tools like Impulse’s SafeConnect which can help in some automation without agent deployment.
Instructions for enabling DPI-SSL vary slightly depending on your SonicOS version, but look for DPI-SSL, Deep Packet Inspection or Decryption Services in the left-hand menu. For testing, create an Address Object that includes a few host machines you would like to test with, and then include this object in your DPI-SSL settings. Once you're happy everything is working, you can easily change this to a broader group.
DPI-SSL Logging Issues
Earlier versions of SonicOS had some logging issues when DPI-SSL was enabled, affecting the accuracy and detail of web traffic in your reports. Fortunately, SonicWall fixed these in SonicOS 6.5.
If you're running SonicOS 6.2.7 and below, please be aware of these two issues:
- SonicWall DPI-SSL Logging Issues Affecting Bandwidth Reports
- SonicWall Logging Issues Affecting Alerts and Reports on Google Searches
Enable Name Resolution
Even if you have authentication enabled, you may have certain traffic excluded from authentication such as Windows and virus updates, guest networks, BYOD devices etc. In these situations, Fastvue Reporter for SonicWall will attempt to resolve the IP addresses, however it is a good idea to get SonicWall to log the resolved IP address instead. This will save the extra lookups from your Fastvue server, and/or any extra DNS configuration that is required for the Fastvue Server to resolve IPs in the first place.
On your SonicWall device, go to Log Settings | Name Resolution and ensure you have a Name Resolution method set, and the DNS servers correctly configured.
Enable Referrer URL Logging:
One of the major inputs to Fastvue's Site Clean engine is referer URLs which SonicWall added support for in SonicOS version 6.2.7.1.
Ensure you are running SonicOS 6.2.7.1 or above, and your logging format is set to 'Enhanced Syslog' with all fields selected (specifically, the 'Notes' field as this is where the referer URL is logged).
SonicWall will then log referrer URLs for http requests which helps the Fastvue Site Clean engine better determine the websites actually visited by your users, and remove/clean the background websites from your reports.
Note: SonicWall released hotfix SonicOS 6.2.7.1-23n–HF187283 to fix an issue where referrer URLs were not logged for DPI-SSL traffic. We believe this has been rolled into SonicOS 6.2.7.3 and above.
Block the QUIC Protocol
Google, owning many web properties as well as a popular web browser with Chrome (currently used by 60% of the population), decided to take web speed into their own hands and introduce a new protocol between their browser and their servers. This is called QUIC and works over UDP.
Although this is great for the web development community generally, it is not great for firewalls as it impacts on the accuracy of logging and reporting. For now, this only affects Google web properties such as YouTube, Google Search and Gmail, but it may be adopted by other websites moving forward.
Fortunately, SonicWall enables you to disable the QUIC protocol for your network, and then Google Chrome will fall back to using normal https.
You can do this via SonicWall's Application Control Advanced page, or use a standard firewall rule to block UDP port 443.
To block QUIC using SonicWall's Application Control:
- Go to Security Services | Application Control (or Rules | Advanced Application Control in SonicOS 6.5 and above).
- Select Category = Infrastructure, and edit the Google QUIC application
- Select Block = Enable
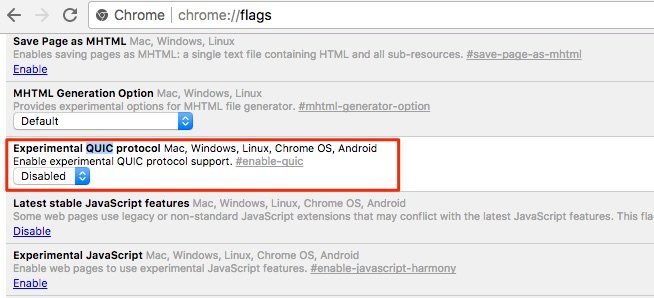
You can also disable QUIC in Google Chrome directly by going to typing chrome://flags in the address bar, and setting the Experimental QUIC protocol to Disabled.
Without the QUIC protocol disabled, you may see inaccurate bandwidth and browsing time figures for Google web properties.
Disable CFS Fast Scan
By default, SonicOS 7.0 enables a hidden feature called CFS Fast Scan by default. This needs to be disabled so that SonicWall logs every URL, not just the first URL in a session. To do this, go to the diag page in your SonicWall’s web interface (https://[ip-address]/sonicui/7/m/diag), and disable the CFS Fast Scan option.
Summary
Getting started with Fastvue Reporter for SonicWall is very easy, but once you start digging into the reports, you may discover issues such as users showing as IP addresses instead of usernames, blank 'search term' reports, blank productivity reports, reports cluttered with advertising and other junk, or inaccurate bandwidth figures.
Ensuring you're on the latest SonicOS (we recommend SonicOS 6.5 and above) and enabling the features above will give you the best configuration from a logging and reporting perspective, and improve your ability to protect and secure your network.
Take Fastvue Reporter for a test drive
Download our FREE 14-day trial, or schedule a demo and we'll show you how it works.
- Share this storyfacebooktwitterlinkedIn
SonicWall Reporting on Users, Departments and AD Security Groups
SonicWall SonicOS Enhanced 6.2.7.1 - Now with Referrer URLs!