Firewall Reporting for Manufacturing: Improving Network Security and Reducing Downtime

by

Bec May
In manufacturing, downtime is not just an IT inconvenience. It is a measurable business cost. Research indicates that the average cost of unplanned downtime in manufacturing is approximately $260,000 per hour, when taking into account lost production, labour, and overhead.
In high-uptime environments where production schedules and delivery commitments depend on continuous workflows, even small disruptions ripple through, leading to lost output, idle labour, overtime costs, delayed shipments, and strained customer relations.
At the same time, modern manufacturing environments are increasingly complex. Production systems, cloud platforms, remote access, supply chain integrations, and distributed sites all rely on stable IT infrastructure and consistently enforced network security controls. Firewalls sit at the centre of this environment, managing traffic, enforcing access controls, and generating detailed log data that reflects how systems and users interact.
Most manufacturing organizations already operate a layered network security stack; however, deploying security controls is only part of the equation. In manufacturing environments, the harder task is maintaining continuous visibility into how bandwidth, firewall policies, and remote access behave in practice. Without structured reporting and real-time insight, performance issues and security risks can remain buried in raw log data until they affect production.
Firewall reporting provides a practical layer of visibility. By turning firewall log data into structured dashboards and time-filtered reports, manufacturing organizations can reduce investigation time, strengthen network security oversight, support governance requirements, and address operational bottlenecks before they escalate into costly downtime.
The Network Visibility Gap in Manufacturing Network Security
Manufacturing environments are rarely simple. On-prem systems coexist with cloud-based applications. IT networks intersect with OT environments. Legacy systems operate alongside newer digital platforms. Supply chain integrations introduce additional access pathways. As these environments expand, the attack surface grows accordingly.
Firewalls play a central role in this environment. Whether deployed at individual plants, at the corporate data center, or between IT and OT networks, they enforce access controls and filter traffic while generating detailed records of every connection and firewall rule decision.
Modern connectivity models add further variability. SD-WAN deployments, aggregated circuits, centralized inspection, remote VPN users, and cloud services all increase the volume and diversity of traffic moving through the firewall.
When bandwidth usage spikes in a production facility, IT teams need clarity. Is the traffic aligned with business operations or non-essential internet usage? Which authenticated user generated it? Which firewall rule allowed it? Is the issue operational, or does it indicate a security concern?
The same applies when unusual traffic patterns emerge or when management requests a structured report on a user’s internet activity. Native firewall logs rarely provide that level of clarity.
Without structured firewall reporting, answering these questions requires time-consuming log analysis that slows investigations and diverts internal resources in environments where production timelines leave little margin for delay.
Structured firewall reporting closes this visibility gap by translating firewall log data into operational views aligned with real-world manufacturing needs.
Transforming firewall data into operational insight with Fastvue Reporter
In manufacturing organizations, visibility needs to be practical. Fastvue Reporter’s structured dashboards provide focused views that align with real operational questions.
Bandwidth visibility across users, departments, and sites
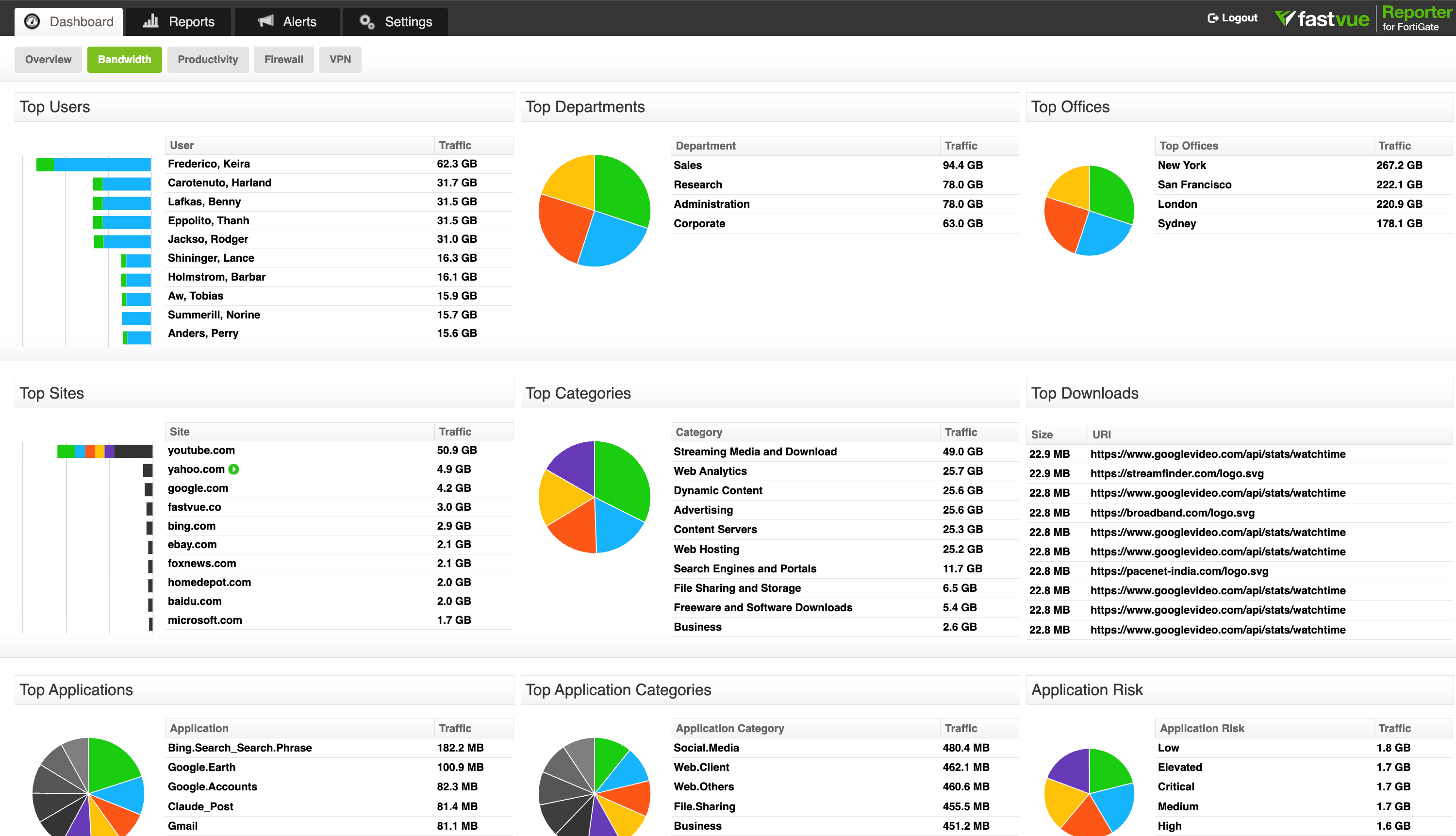
The Bandwidth Dashboard provides a structured overview of how network traffic is distributed across the organization. Instead of manually reviewing raw firewall logs, IT teams can immediately see which users, departments, and offices are consuming the most bandwidth, including:
Top users by traffic volume
Department-level bandwidth usage
Traffic by office or site
Most visited websites
Top traffic categories
Largest downloads
Application usage and associated risk levels
In distributed manufacturing environments, this level of visibility matters. A spike in streaming media traffic or large external downloads during peak production hours can affect shared circuits. Identifying those patterns quickly allows internal teams to address congestion before it impacts operational systems.
The inclusion of application risk categories also provides additional context. IT teams can see not only how much traffic is flowing but also whether it is associated with low-, medium-, or high-risk applications. This supports stronger network security while maintaining operational awareness.
Productivity Dashboard: Categorized internet usage and policy oversight
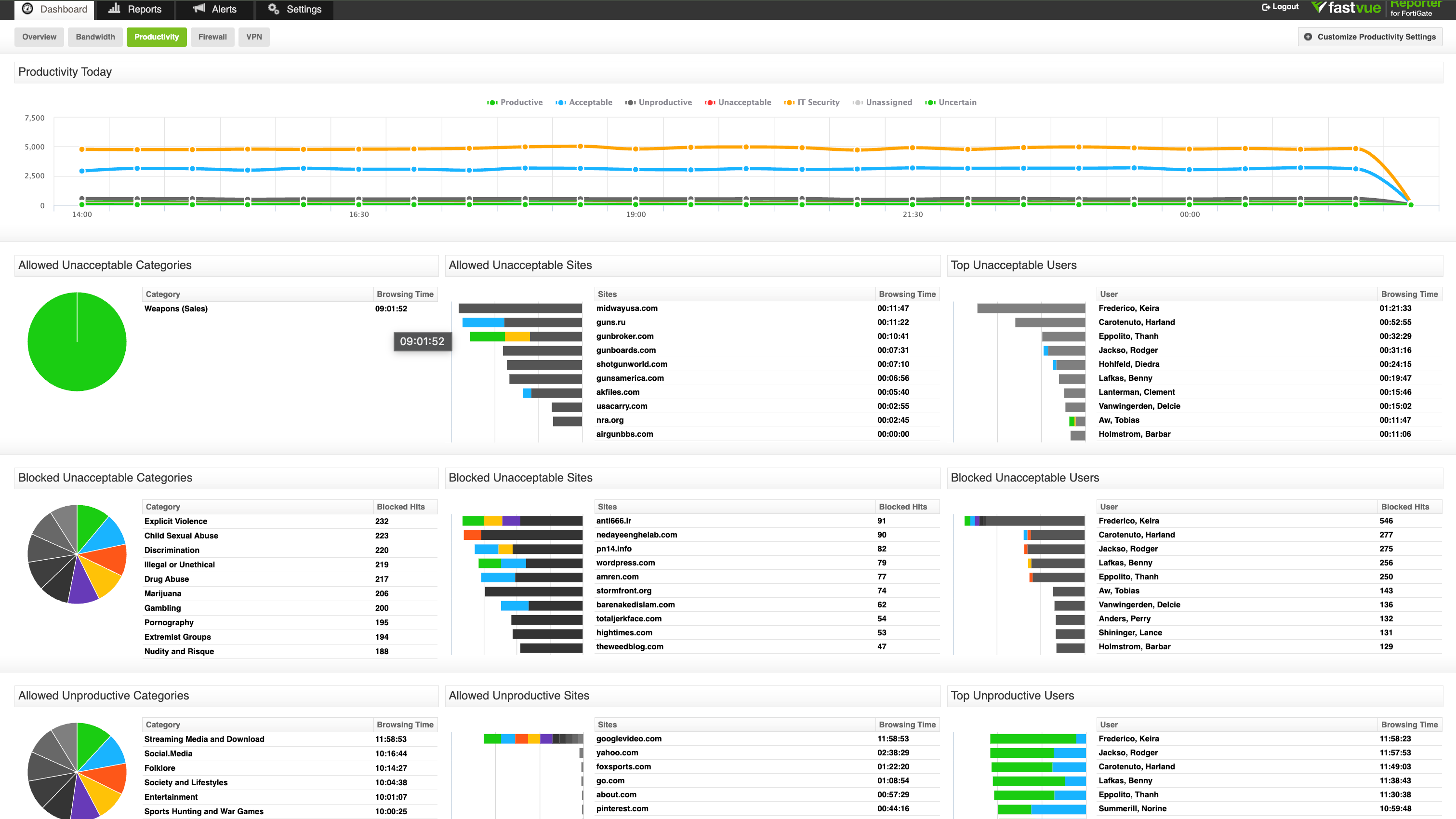
The Productivity dashboard provides structured insight into how internet activity aligns with the organization's defined acceptable use policies.
The dashboard highlights:
Time spent in allowed unacceptable categories
Blocked unacceptable categories and sites
Top users accessing unacceptable sites
Allowed unproductive categories
Top unproductive users
For internal IT teams, this provides a balanced view of both performance and policy enforcement.
In manufacturing environments where administrative teams, production supervisors, and remote staff share infrastructure, this categorised visibility supports clearer conversations around acceptable use without requiring manual investigation.
It also reinforces access control governance. Repeated blocked attempts or sustained time spent in high-risk categories can indicate policy gaps or behavioral patterns that require review.
Rather than acting as a surveillance tool, the Productivity view supports structured oversight. It gives manufacturing organizations measurable insight into how internet usage aligns with operational expectations and network security policies.
Firewall Dashboard: Security threats, firewall rules, and blocked activity
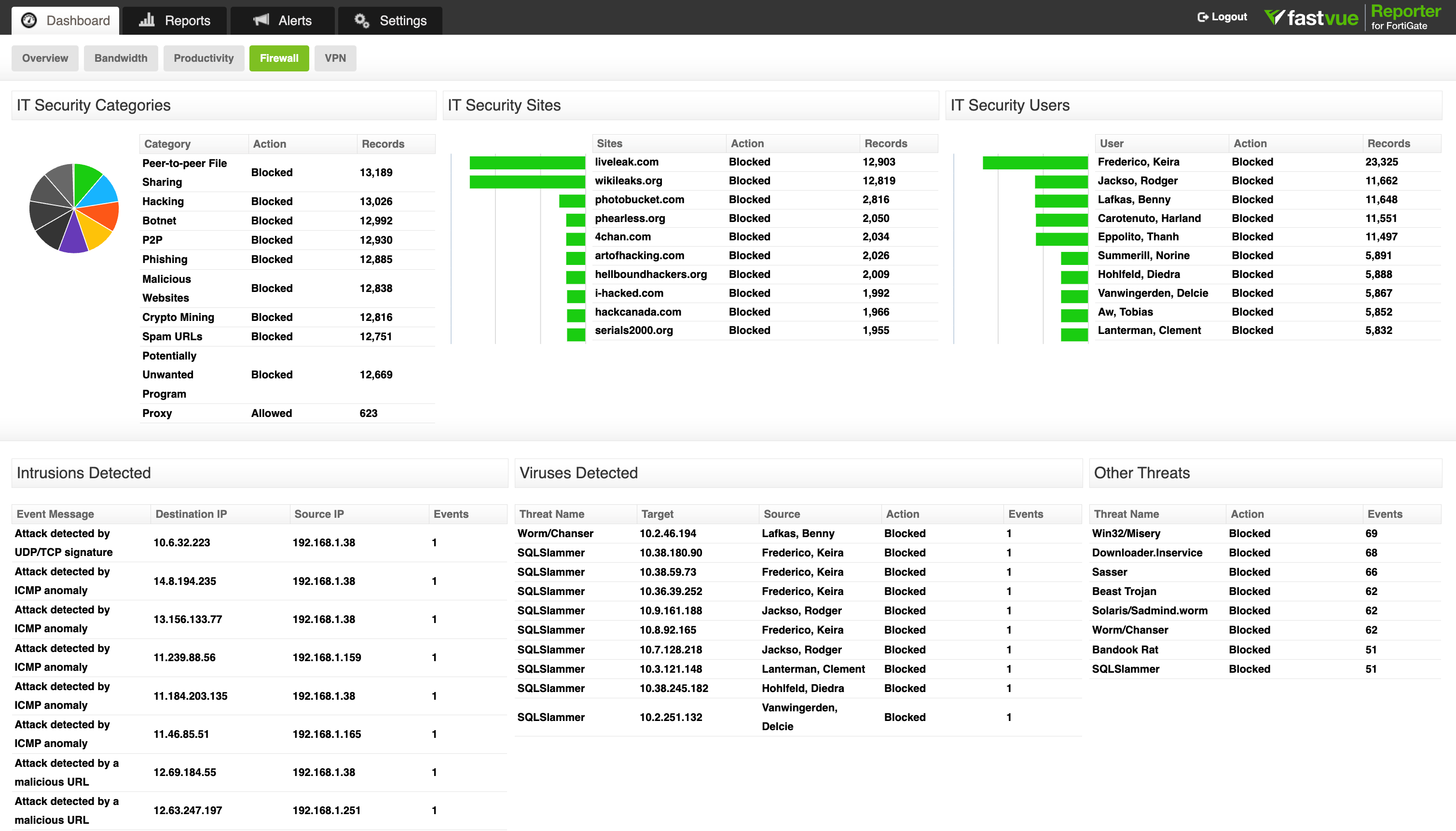
The Firewall Dashboard provides structured visibility into how security controls operate across manufacturing environments. It consolidates firewall actions, threat detections, and rule enforcement into a single operational perspective.
At a glance, internal IT teams can see:
Allowed, blocked, and dropped traffic
Activity by web filter and application profiles
IT security categories such as phishing, botnets, malware, peer-to-peer sharing, and crypto mining
Intrusions detected by signature or anomaly
Viruses identified and blocked
This view closes a common visibility gap. Firewalls generate significant log data, but without structured reporting, it is difficult to interpret trends or identify security gaps.
For manufacturing organizations operating across IT and OT environments, this matters. Threat activity targeting legacy systems, unpatched services, or exposed services in distributed plants can surface in intrusion logs long before it becomes a security breach.
Fast incident response and strong security assessments hinge on the ability to see:
Which categories are most frequently blocked
Which users or departments trigger security events
Which threats are repeatedly detected
How firewall rules are applied in practice
Rather than treating firewall monitoring as a reactive function, this structured visibility enables proactive oversight. It allows internal teams to validate that access controls are working as intended, identify potential vulnerabilities, and reduce the attack surface without introducing another complex cybersecurity platform.
VPN Dashboard: Monitoring remote access
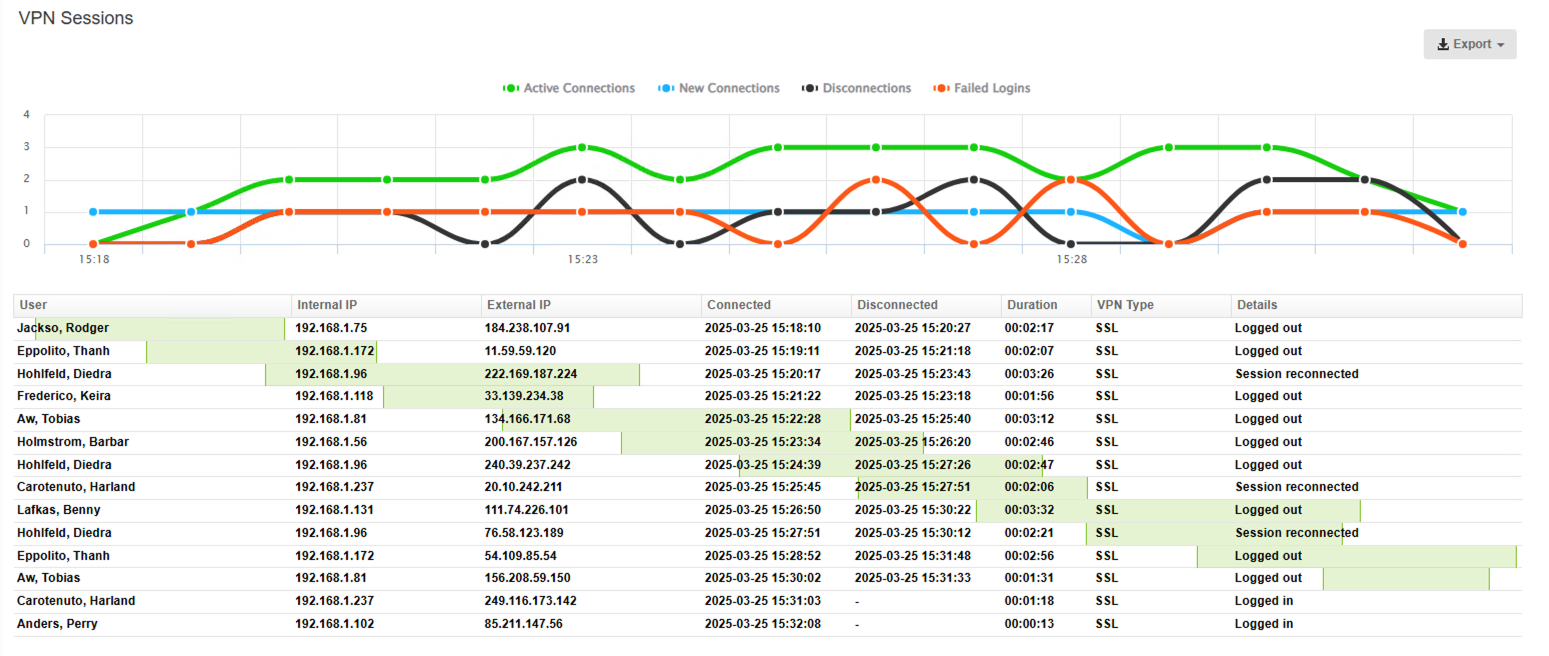
Remote access is now standard across the manufacturing industry. Engineers, supervisors, vendors, and third-party partners frequently connect to production systems and enterprise platforms through VPN.
The VPN dashboard provides real-time visibility into:
Active VPN connections
New and disconnected sessions
Failed login attempts
User-level session duration and data volume
Source IP addresses for failed authentication
For manufacturing organizations managing distributed sites and supply chain relationships, this visibility strengthens access control governance.
A spike in failed logins may indicate misconfigured credentials, unauthorized access attempts, or brute-force behavior. High data transfer volumes from remote sessions can warrant review when intellectual property or production systems are involved.
By consolidating connection data, disconnections, and authentication failures into a single view, internal IT teams can quickly assess whether VPN activity aligns with expected operational behavior or indicates a potential security risk.
Strengthening network security fundamentals without adding complexity
Manufacturing companies already invest in layered network security strategies that include endpoint protection, patch management, network segmentation, and access controls. These controls protect production systems, intellectual property, and customer data across distributed environments.
For most internal IT teams in multi-site manufacturing environments, the challenge is not defining the right controls; it is maintaining oversight with limited internal resources.
Introducing another complex cybersecurity platform rarely solves that problem. In many cases, it increases operational overhead. What teams often need is clearer visibility into how existing firewalls, access controls, and network policies are functioning in practice.
Improving visibility strengthens established controls without expanding the security stack.
How manufacturing IT teams use firewall reporting solutions
In conversations with IT leaders across the US manufacturing industry, a consistent pattern emerges. Firewall reporting is not typically introduced as part of a major security overhaul. It is added to solve practical operational challenges inside existing network security environments.
Time-bound reporting for management and audit oversight
When supervisors, compliance officers, or executive teams request clarity around internet usage or access controls, real-time dashboards are not always sufficient. Manufacturing organizations often require time-bound, exportable reports that summarize activity across specific users, departments, or sites.
Structured firewall reporting allows IT teams to generate clean, historical reports without manually parsing log data. These reports support:
• Internal HR and management reviews
• Policy enforcement discussions
• Traffic and productivity analysis across manufacturing sites
• Documentation for governance or security assessments
In distributed manufacturing environments, the ability to produce structured reports quickly reduces administrative burden and strengthens accountability.
Firewall monitoring with user directory integration
User investigation workflows are similarly practical. When unusual traffic appears, activity is automatically mapped to the user directory usernames and departments. IT teams do not need to chase IP addresses or cross-reference devices. They can see which authenticated user account generated the traffic and which firewall rule applied to it.
Many manufacturing IT teams operate with small headcounts and broad responsibilities. They are looking for solutions that work with the existing firewall infrastructure, support on-prem deployment where required, and deliver structured visibility without requiring a dedicated analyst.
For many manufacturers, firewall reporting functions as the operational visibility layer that these environments are missing.
This level of identity-based visibility reduces investigation time and removes ambiguity. In manufacturing environments where production continuity matters, a delay in understanding network activity can escalate quickly. Being able to move from a traffic spike to a named user account and associated firewall rule in minutes, rather than hours, improves both operational stability and security oversight.
Quickly identifying security threats and firewall activity
For many manufacturing companies, real-time visibility into what's happening on the firewall is just as important as longer-term reporting to identify patterns of use across the network.
Real-time dashboards make clear:
Which security threats are being blocked
Which firewall rules are being triggered
Where access policies are allowing or denying traffic
Whether unusual outbound traffic patterns suggest emerging cyber risks
In manufacturing environments where supply chain integrations, remote vendors, and cloud services introduce additional access pathways, maintaining awareness of firewall rule behavior strengthens the overall security posture and supports faster review when a suspected security breach requires investigation.
While firewall reporting does not replace dedicated threat detection platforms, it supports ongoing security assessments by providing clear insight into traffic patterns, blocked malware, and rule enforcement across distributed sites.
For manufacturing companies handling intellectual property and sensitive operational data, understanding how traffic moves through the firewall reduces uncertainty and strengthens control.
Supporting manufacturing compliance expectations
A single regulation doesn’t cover cybersecurity obligations in US manufacturing. Organizations operate at the intersection of contractual requirements, industry frameworks, and supply chain expectations. Federal contractors may align with CMMC or NIST 800-171 controls; publicly traded manufacturers must consider governance and reporting standards; and others follow ISO-based frameworks.
Across these models, several common expectations appear:
Documented access controls
Log retention and monitoring
Evidence of firewall rule enforcement
Defensible incident response processes
Audit-ready reporting
These frameworks do not typically mandate a specific firewall reporting tool. What they require is demonstrable oversight.
Structured firewall reporting supports this by turning raw firewall log data into usable documentation, enabling manufacturing organizations to retain historical activity, demonstrate traffic monitoring, validate access control enforcement, and produce clear audit-ready reports when required.
Next Steps
Fastvue Reporter provides a focused reporting layer built for manufacturing environments where uptime, accountability, and operational clarity matter. It deploys on-prem or in a private cloud environment and integrates directly with the world’s leading firewall brands, so there is no need to replace your existing infrastructure. Get started with a free trial today and get the clarity your IT team needs.
FAQs
Join top organizations using Fastvue Reporter
Download Fastvue Reporter now and try it free for 14 days or schedule a demo and we'll show you how it works.
- Share this storyfacebooktwitterlinkedIn

